
The Most Trusted Network
Vulnerability Assessment Services
Why Do You Need Network Vulnerability Assessment Services?
Modern corporate networks encompass multiple routers, switches, firewalls, hubs, servers, and load balancers. They include subnets, VLANs, WANs, and connections to the public internet as well.
These complex interconnections between many network devices result in a myriad of potential entry points and vulnerabilities. Attackers can use these network vulnerabilities to gain access to your backend servers and sensitive business systems.
If you want to protect your company and your customer base, you should utilize powerful network vulnerability scanning and assessment processes to scan your entire network. This will help you discover whether any vulnerabilities are present in your network and diagnose any security holes that need to be patched.
This is one of the first steps that our network security testing engineers take to gauge the security posture of your network. This helps us determine how well we can defend and reduce the attack surface on your network and how efficiently we can help you mitigate threats.
When performing vulnerability assessments according to the most comprehensive security methodologies, our managed security testing services include multiple phases:
- Footprinting/recon
- Port and vulnerability scanning
- Exploitation
- Post-exploitation
With our specialized network vulnerability assessment services, you will get invaluable data about your network's security posture.
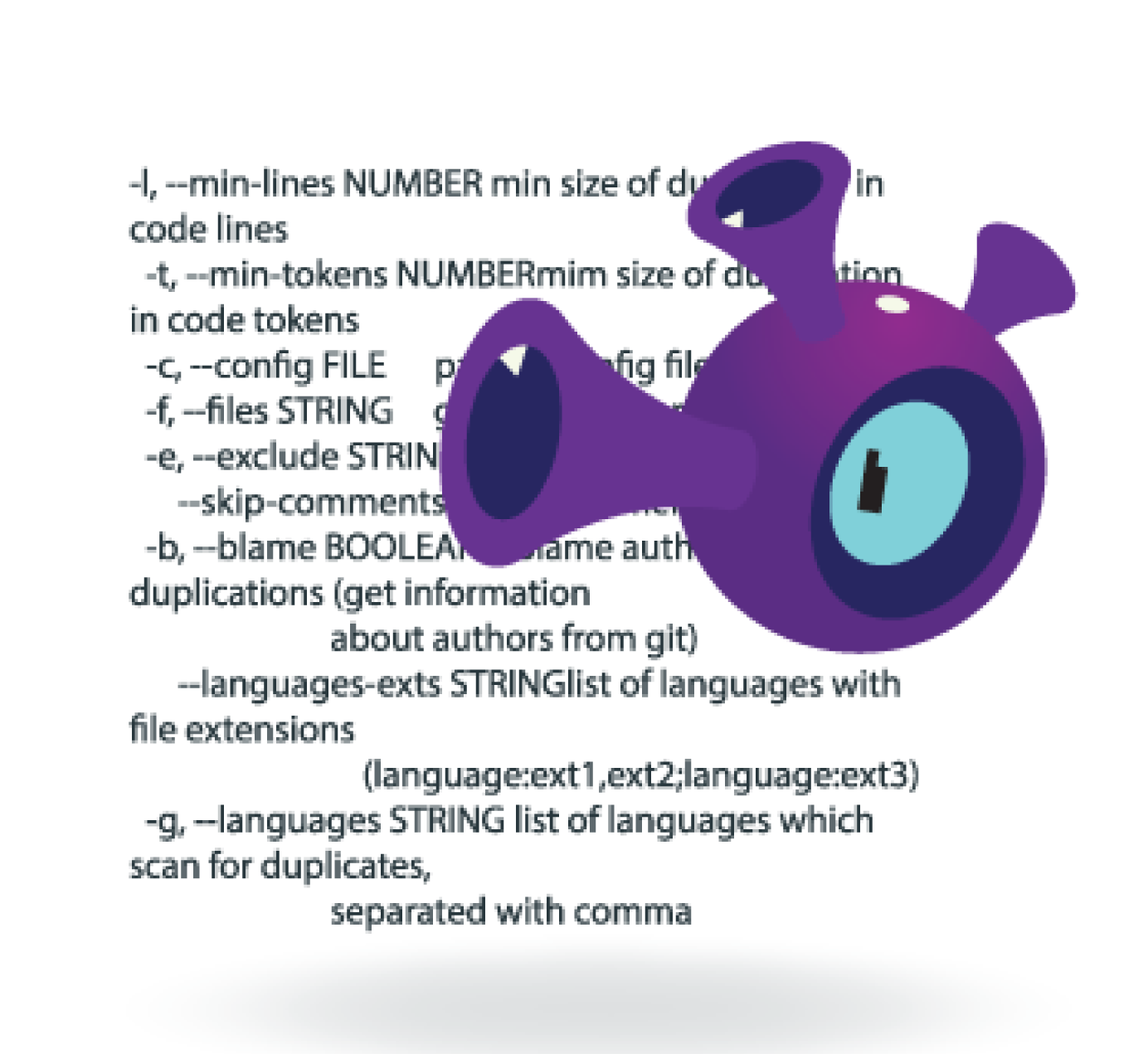
Our expert team of security personnel uses the most powerful proprietary and open-source vulnerability assessment tools along with manual testing to give you a complete overview of the activity of your corporate networks. The tools we use include:
- Automated tools that identify and enumerate network devices (servers, routers)
- Ports (open TCP and UDP ports)
- Services
- Patch levels
- Configurations
- And much more
Along with the use of Simple Network Management Protocol (SNMP) and Port scanners, these complex security mechanisms give great visibility into the state, functionality, and efficacy of your network. This can help you make informed decisions on patching, configurations, and hardening, and help you ensure data security.
We believe that one needs to think like a hacker in order to conduct vulnerability scanning and maintain data security. Therefore, our security experts carry out the same tests on your system that a hacker would, and more.
That’s how our network vulnerability assessment services help you ensure that your networks are secure.
Powerful Network Vulnerability Assessment Services
When reviewing your network for vulnerabilities, we conduct a thorough assessment to determine if any known vulnerabilities exist and if any unpatched systems exist that could allow for cyber attacks.
We also assess if there are any system misconfigurations, exploitable programs, insecure devices, or vulnerable scripts running on your business systems.
That’s because the configuration of your servers, routers, switches, and other network devices - along with the appropriate use of 802.1x, intrusion detection and prevention systems (IDPS), firewalls (with access control lists), and network access control - largely determine how secure your network will be.
Therefore, our security testing engineers check your system for the aforementioned security controls and their correct configuration.
We conduct both authenticated and unauthenticated vulnerability scans on your networks to identify potential entry points.
Here’s what we do when conducting these two scans on your networks:
Authenticated Scan
This type of vulnerability scan focuses on areas of the network that a logged-in, authenticated user with internal knowledge of access to the system can exploit.
We use this scanning process to conduct a more detailed, widespread assessment, expose weaknesses, and determine the threat level of a malicious internal threat.
This testing method allows for the utilization of more network ranges, including VLANs, subnets, host systems, and other IP addresses usually associated with the purview of an authenticated user.
Going back to offensive security methodologies consisting of footprinting, port and vulnerability scanning, exploitation, and post-exploitation, authenticated vulnerability scanning allows our security experts to focus less on the discovery phase of the offensive security methodology.
Instead, it allows our engineers to focus on the vulnerability assessment and identification phase.
Unauthenticated Scan
This type of vulnerability scan covers the portions of a network that an unauthenticated user such as an external cyber attacker can access.
Unauthenticated users can only access certain, basic areas of any corporate network. Cyber attackers utilize session hijacking, man-in-the-middle attacks, code injection, or malware such as rootkits and backdoors to access databases, information, resources, servers, and files.
Along with pivoting through different systems, these attackers can also use rootkits and tools for privilege escalation to gain access to other, more sensitive systems, all from initially being an unauthenticated user on the outside of your network.
Though unauthenticated users may be able to initially access only limited parts of your network, if they can get a foothold, they can represent a very real threat to your business infrastructure.
During an unauthenticated vulnerability scan, our security engineers start with little knowledge of the system being tested. We use normative footprinting methodologies to obtain information on the organization and to discover as much about the network as possible.
This usually entails using Google, Google Dorks, WHOIS, and other resources such as dig to obtain DNS information, emails, IP addresses, and policy information.
Along with a port and vulnerability scan, these steps offer a good simulation of what an attacker could potentially use to expose your business system and exploit it.
Conducting both authenticated and unauthenticated vulnerability scans enables us to provide a comprehensive security overview of how well your business network will stand up against an external or internal threat.
You can find out the different attack patterns associated with internal and external threats, and consequently, harden your systems to ensure complete data security with our detailed network vulnerability assessment services.
BRANDS THAT TRUST US




WHY CHOOSE US?
Any specific points or should we use the already available ones?
We are security experts who train others.
Our network security specialists regularly instruct for large corporations and global training institutions. We teach developers and organizations on how to properly assess their networks for security vulnerabilities.
We are all developers and we understand code.
We aren’t only experts in security, we also know how applications are (and SHOULD be) built. We can leverage this knowledge to provide the most thorough security reviews for your applications as well as networks.