
NETWORK PENETRATION
TESTING SERVICES
Protect Your Networks Through Specialized Penetration Testing Services
With emerging technologies and architectures, cybersecurity has become a complex landscape. Malicious attackers are ready to exploit network vulnerabilities to gain access to information, take over networks, install malware, disrupt services, and more.
Will your security controls and defenses stand up to the test? Do they meet industry standards? You can conduct a network penetration test with us to find out.
During penetration testing execution, our security engineers will actively identify vulnerabilities to examine the actual effectiveness of your existing security controls against an active, skilled attacker.
Once they identify security vulnerabilities, they will look to exploit those vulnerabilities to compromise the systems and then look to pivot further to get deeper into the system. With permission, such post-exploitation activities can include the use of rootkits and malware (armored viruses, backdoors, polymorphic viruses, etc.).
Our specialized network penetration testing services go a step beyond simple vulnerability scanning. We not only scan your networks for security holes but also help you determine the efficacy of your security controls.
These security controls include:
- Monitoring systems such as Network/Host Intrusion Detection Systems (NIDSs/HIDSs) and Intrusion Detection and Prevention System (IDPS)
- Comprehensive log systems such as access logs, system logs, traffic logs, etc.
- Defensive fronts such as Unified Threat Management or Next-Generation Firewall, Web Application Firewall (WAF), Network and Host Firewalls, etc.
- Corporate encryption systems
This can help you get a thorough and comprehensive overview of your company's network security posture.
Powerful Network Penetration Testing Services
Our security engineers simulate real-life attacks using a variety of tools and good old manual attack techniques. We use methodologies similar to those used by a malicious attacker to attack your systems, bypass security controls, and gain access to your systems.
This helps us identify network security vulnerabilities, determine the efficacy of security controls, and test the security of your corporate systems.
Here’s how using a combination of automated and manual penetration testing techniques helps us identify the vulnerabilities in your networks:
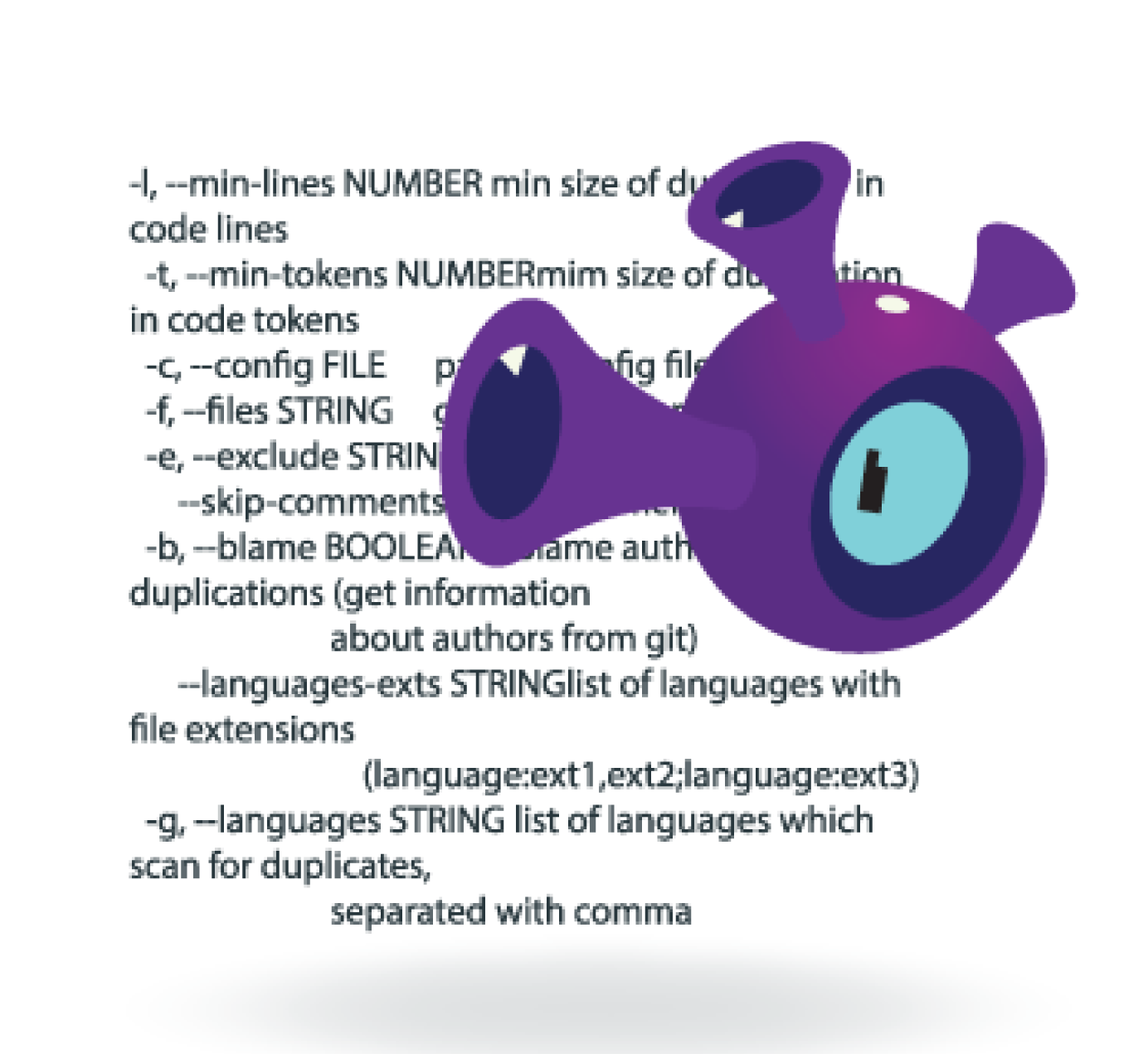
- Automated tools can include various testing platforms alongside proprietary and open-source tools and frameworks.
These tools are used to identify system vulnerabilities and to execute exploits to take advantage of system weaknesses. This offers a quick and easy way to test a system, but automated tools alone are not enough for penetration testing. It is also important to conduct manual testing by humans. - Manual methods include code injection, adapted shell scripting, malware usage, and other advanced techniques.
This offers a more in-depth penetration testing that can result in the use of uncommon attack vectors, giving your company a better, more realistic view of a real-life attack.
Manual testing uses proprietary methodologies, custom exploits/payloads, and scripts to compromise systems, account passwords, sensitive data, etc. This penetration testing methodology also allows security engineers to verify the findings of automated scanning tools in order to eliminate false positives.
Combining the mechanisms and methodologies mentioned above allows us to conduct a comprehensive penetration test. Deep network penetration testing services help us cover a majority of attack surfaces. Our network security engineers also give you a complete overview of your security posture and an actionable report that helps you hit the ground running.
Have our security experts uncover the attack surfaces and vulnerabilities in your systems by conducting a network penetration test.
BRANDS THAT TRUST US




WHY CHOOSE US?
We offer specialized network penetration testing services.
We are security experts who train others.
Our application security specialists regularly instruct for large corporations and global training institutions. We teach developers and organizations how to properly perform application and network penetration testing to ensure that their networks are secure.
We are network security engineers.
We aren’t only experts in security, we also understand how malicious attackers can gain access to your network. We can leverage this knowledge to conduct penetration testing and provide the most thorough security reviews for your networks as well as applications.