
WEB APPLICATION
STATIC ANALYSIS
Your web applications are made from code. Don’t you think it’s a good idea to check out that code to make sure it’s secure?
Yes, dynamic web application penetration testing is useful when it comes to identifying security vulnerabilities. However, reviewing the source code can help you identify its weak defenses within minutes. You need to do both static and dynamic analysis of your web applications.
Why not go to the experts for static analysis?
We have coded for years, and we know how applications are (and SHOULD be) built. We can help you ensure that your applications are secure.
SUFFERED A DATA BREACH DUE TO INSECURE WEB APPLICATIONS?
Web applications are everywhere. Unfortunately, these applications are increasingly targeted to breach a corporate network.
In fact, 60% of the time, a vulnerable web application is the attack vector that leads to a data breach. 25% of companies confirmed or suspected a data breach due to a web application this year alone. These are the ones who know/suspect it!
To prevent such data breaches, it’s crucial for organizations to ensure that their applications are secure.
Most organizations conduct dynamic web application penetration testing using various tools and software solutions. While dynamic application security testing (DAST) can help you identify security vulnerabilities in your applications, it’s not enough.
Dynamic testing doesn’t provide insights into:
- Whether the cryptography is secure.
- How passwords are stored.
- How system passwords are stored.
- What server side calls are being made and if they are secure.
It could take a dynamic PEN tester hours or days to bypass a specific security controls. But ,by looking at the code, you can easily identify its weaknesses.
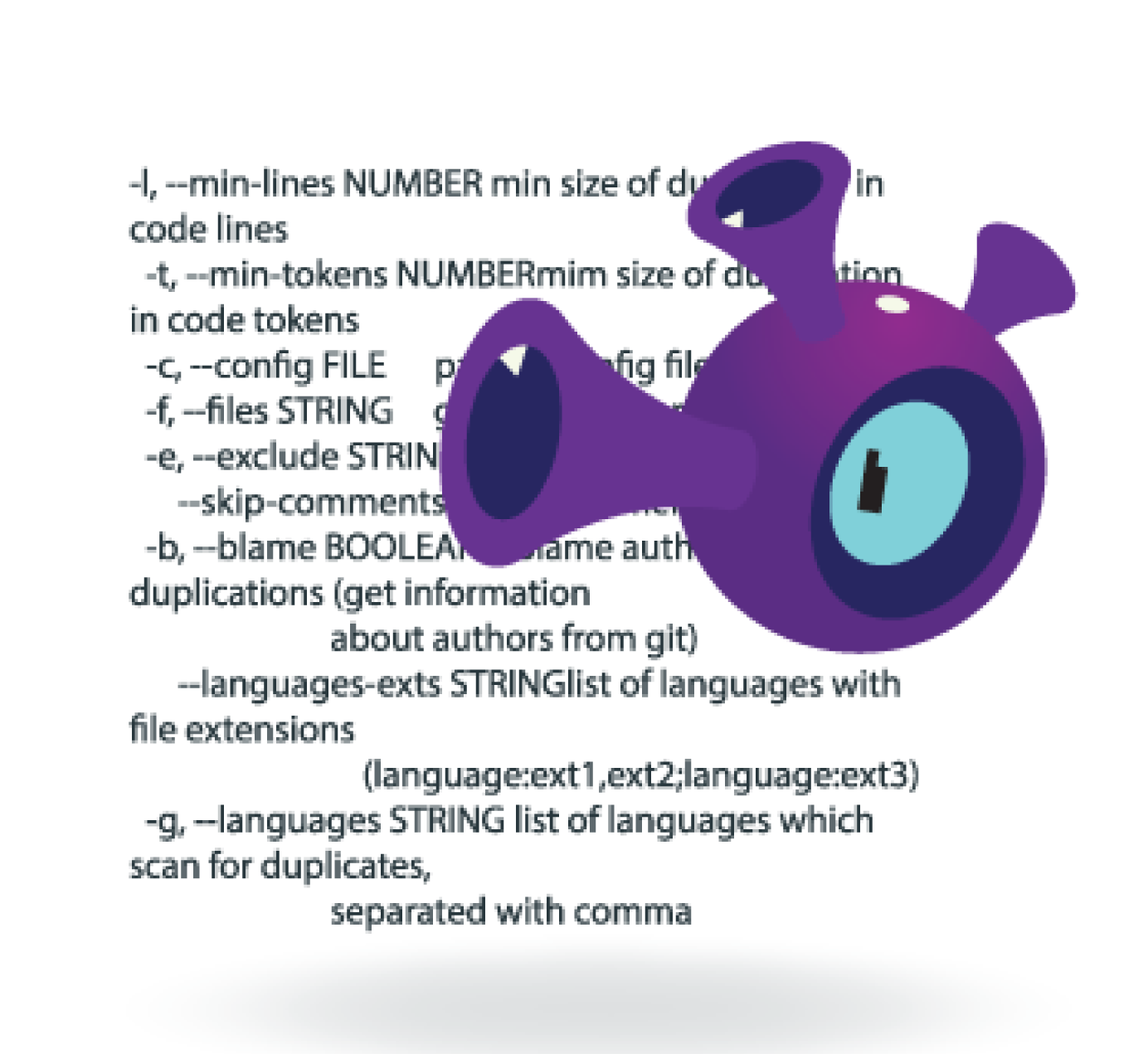
Want to review the code using static analysis (SAST)? Then, you’re in the right place.
We are security experts, and we understand code.
SPECIALIZED WEB APPLICATION STATIC ANALYSIS BY THE EXPERTS
Modern web application development relies on web frameworks. These frameworks offer pre-written code for standard components such as user interface design and database management. This allows developers to concentrate on developing other features and functions of the app.
Web frameworks can often introduce security issues into your web applications. You need to conduct static analysis to review the entire source code to mitigate such risks.
We know how to review code. We have decades of experience doing this, and we regularly assess web applications for security threats. Our security specialists not only know how to see the vulnerabilities in your apps, but can also recommend the best practices to fix your code.
Our security engineers regularly instruct for large corporations and global security training companies, and we can help train your developers to recognize security defects. We can help you develop a secure software development cycle (SSDLC) to ensure that your web applications are secure.
BRANDS THAT TRUST US




WHY CHOOSE US?
We can conduct static analysis to thoroughly review the code of your web applications for security issues. With our specialized penetration testing services, you can rest assured that your apps are secure.
We have years of coding experience.
We know how to develop secure code, and we regularly assess applications.
We are all developers and we understand applications.
We aren’t only experts in security, we also know how applications are (and SHOULD be) built. This knowledge helps us thoroughly test your applications with static analysis (SAST).
We are security experts who train others.
Our application security specialists regularly instruct for large corporations and global security training companies. We teach people how to design and develop secure code.