MOBILE APP
HYBRID ANALYSIS
Compromised mobile applications can lead to huge losses. A data breach can cost an average of $3.9 million to organizations. That’s why mobile app security is essential.
Have our experts conduct a hybrid analysis to ensure that your apps are secure.

Want to Secure Your Mobile Applications?
You are probably reading this on a mobile phone, right?
With over 3 billion smartphone users worldwide, mobile devices have become mainstream platforms for both personal and business operations and communications. Their usage in buying and selling items and social media communications will continue to grow.
This escalation of mobile devices and the market surrounding mobile apps has created an opportunity for businesses to develop apps that their consumers can use.
However, this rush to market has also generated an unprecedented number of cyber-security vulnerabilities and threats to the devices, users, and the IT infrastructures associated with these mobile applications.
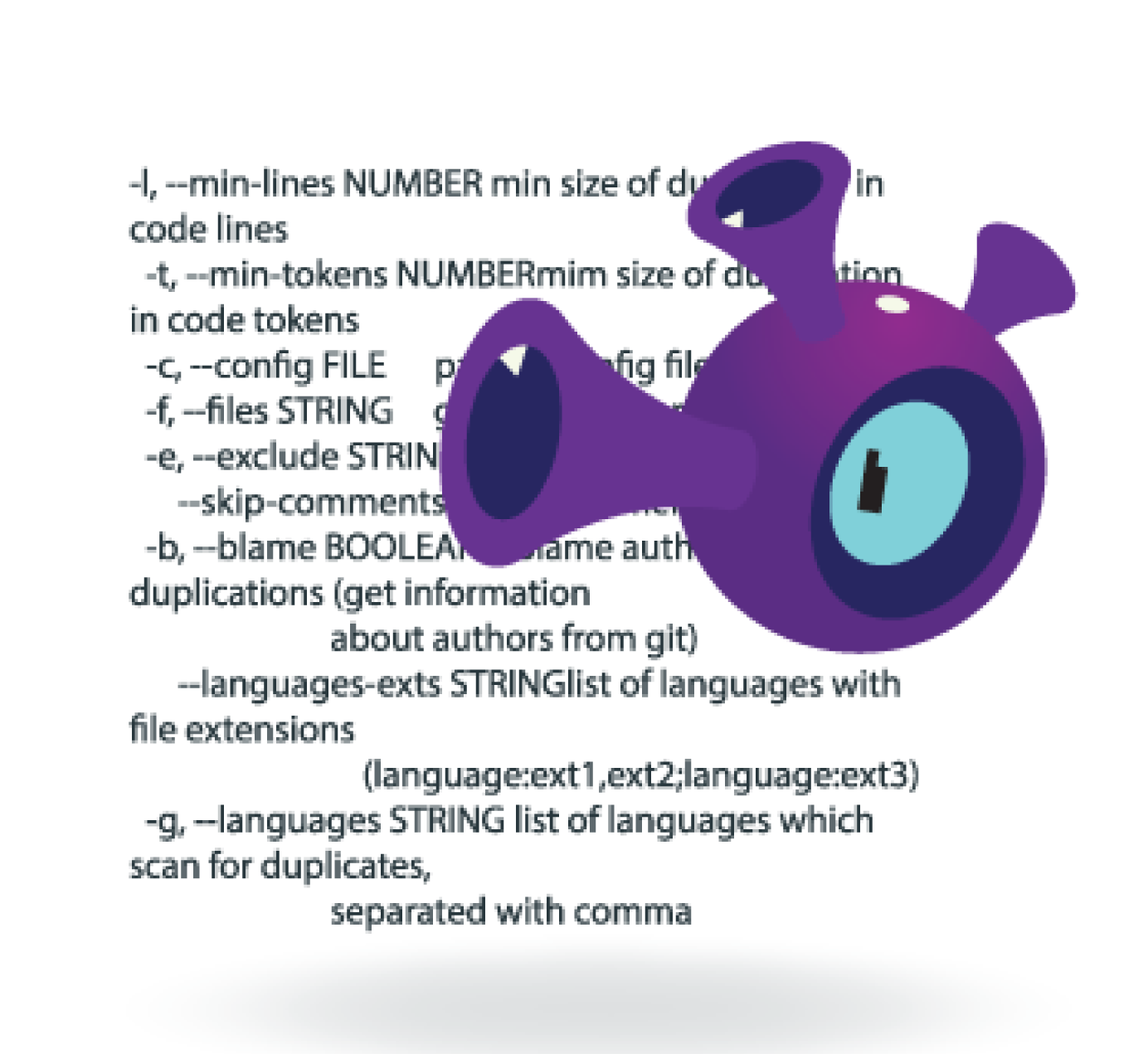
Companies need to assess their mobile applications for security. Our security engineers can perform both dynamic and static security assessments of your applications to identify risks before attackers do.
This includes both automated scanning and penetration (pen) testing of applications, along with manual and automated source code reviews.
Have our experts conduct a thorough hybrid security analysis of your mobile applications.
Powerful Hybrid Analysis Services for Risk Assessment
Relying solely on either pen testing or source code reviews can cause you to miss potential security threats. A mobile app penetration test can find certain vulnerabilities that a static code review might miss and vice versa.That’s why our security engineers recommend that you opt for hybrid analysis services.
Simultaneously pen testing and reviewing the source code of your mobile applications can help uncover a greater attack surface. A dual-method approach can help you identify multiple potential vulnerabilities that any one method would not sufficiently uncover. This can reduce potential attack vectors in your mobile apps and help you mitigate threats.
Our security engineers use cutting-edge, hybrid analysis tools and methodologies to give you a multi-faceted view of the security posture of your mobile application.
We provide a comprehensive security overview of your application at runtime using automated tools and frameworks and manual testing. We also thoroughly review the source code of your application to discover vulnerabilities that exist.
Our hybrid analysis reports provide you with valuable information on the current security posture of your mobile apps. This information can help developers utilize more secure coding practices in the future, and contribute to developing a secure software development lifecycle (SSDLC).
Strengthening your mobile application development process can not only increase efficiency but also reduce overhead costs and save time. Following secure coding practices will automatically result in fewer security flaws in your applications and mitigate threats.
Have our experts conduct a thorough hybrid analysis of your mobile apps.

BRANDS THAT TRUST US




WHY CHOOSE US?
Have our security specialists conduct a hybrid security analysis of your mobile applications.
We are security experts who train others.
Our application security specialists regularly instruct for large corporations and global training institutions. We teach developers and organizations how to properly combine mobile application penetration testing and source code review.
We are all developers and we understand code.
We aren’t only experts in security, we also know how mobile applications are (and SHOULD be) built. We can leverage this knowledge to provide the most thorough security reviews of your mobile apps.We can also help you develop a secure software development lifecycle (SSDLC) for your mobile applications.