THE MOST TRUSTED APPLICATION SECURITY TESTING SERVICES
IS APPLICATION SECURITY YOUR WEAK POINT?
Most organizations go through extensive measures to secure their networks, but then create applications that expose their sensitive data and critical infrastructure. Unfortunately, most of these applications also contain vulnerabilities.
There’s a need to ensure that your web application security is robust, otherwise, you may be compromising your application as well as your networks.
A majority of security personnel come from network and infrastructure backgrounds, but only a few come from the software and development side. This is a primary reason why web application security is a weak point for many organizations.
In fact, the U.S. Department of Homeland Security stated that 90% of security incidents occur due to failures in application security.
Want to reduce security vulnerabilities in your applications?
You’re at the right place!
LEVEL UP YOUR APPLICATION SECURITY WITH OUR TESTING SPECIALISTS

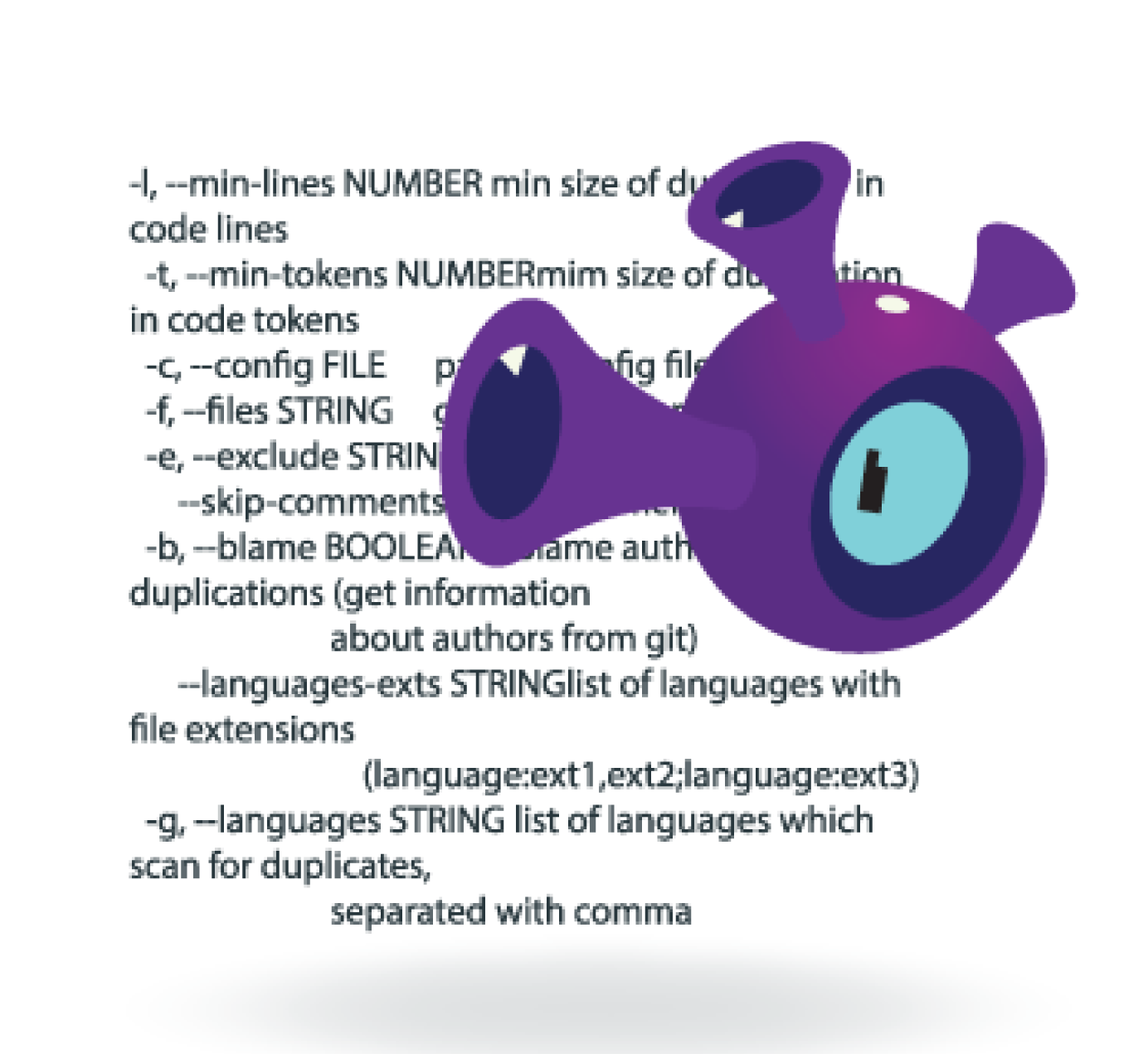
• Static (white-box) testing: With extensive experience in software and development, our testing specialists can efficiently review code to identify vulnerabilities in your applications.
• Dynamic (black-box) testing: Our experts also perform dynamic testing against running applications (application penetration tests / dynamic analysis)
By using automated DAST (dynamic application security testing) and SAST (static application security testing) tools in conjunction with our expertise in manual testing, we leverage the best of each security testing methodology to identify and mitigate risks in your applications, and offer tailored strategies to fortify your security posture.
BRANDS THAT TRUST US




WHY CHOOSE US?
With our application security testing services, you can rest assured that your applications are secure.
We understand code and how applications are built.
All of our security engineers have extensive experience in software development. We understand code. This knowledge enables us to thoroughly understand how your application works and how to best test your applications to identify security vulnerabilities.
We are security experts.
Our engineers regularly instruct for SANS, where they teach developers and organizations how to build and test their applications to ensure they are secure.
We are versatile.
Our engineers test critical applications across numerous verticals, which include intelligence, defense, finance, insurance, healthcare, and other industries.