Application Security
Assessment Services
Sure, you could have some random person, who once read a CISSP book, run an automated security assessment tool on your web and mobile applications.
Or, you could trust our experts, who regularly teach others how to perform application penetration testing and who themselves regularly perform in-depth security assessments.
Have our experts secure your web and mobile applications.
So, Your Organization Gets Breached. Do You Really Care?
Most companies take extensive measures to secure their networks, but then they open their networks to expose their applications.
Most security professionals grow up in the networking and infrastructure world and have limited exposure to software development. Software developers focus more on delivering functionality and speed to market, instead of security.
Do you really trust the security of these web and mobile apps that you opened these ports to run on your network?
Data breaches can have devastating and long-term financial consequences. I am sure you don’t want to damage your reputation, lose customers, lose revenue, or lose your competitive advantage.
That’s why you need to invest in exclusive application security testing and assessment services. After all, no one does it better than the experts.
Development teams usually aim to build fully-functional apps quickly, and security is low on their list of concerns.
Do you want a development team who doesn’t care about application security, to handle the responsibility? Or, do you want the experts, who focus on application security, to handle it?
Our security testing experts can not only ensure that your web and mobile apps are secure at a point of time, but also help your team develop secure apps.
Call us. Our application security testing experts are here to help you.
Secure Your Applications with Our Security Assessment Services
Most security companies simply test apps by conducting application penetration testing and assessment against a running application.
That’s great, but they might be missing out on many security vulnerabilities that only a secure source code review can find (passwords, cryptographic issues, weak XSS defenses, and many more).
We, on the other hand, not only do application penetration testing but also do source code analysis to detect vulnerabilities.
Remember, our application security assessment experts come from a development background. We can find the issues and vulnerabilities that others can’t as they don’t review the source code or they don’t understand it as we do.
With extensive experience in development, our security engineers know best how to identify the weak points in your app security. Along with providing the most thorough security assessment, we also suggest ways to enhance your application security.
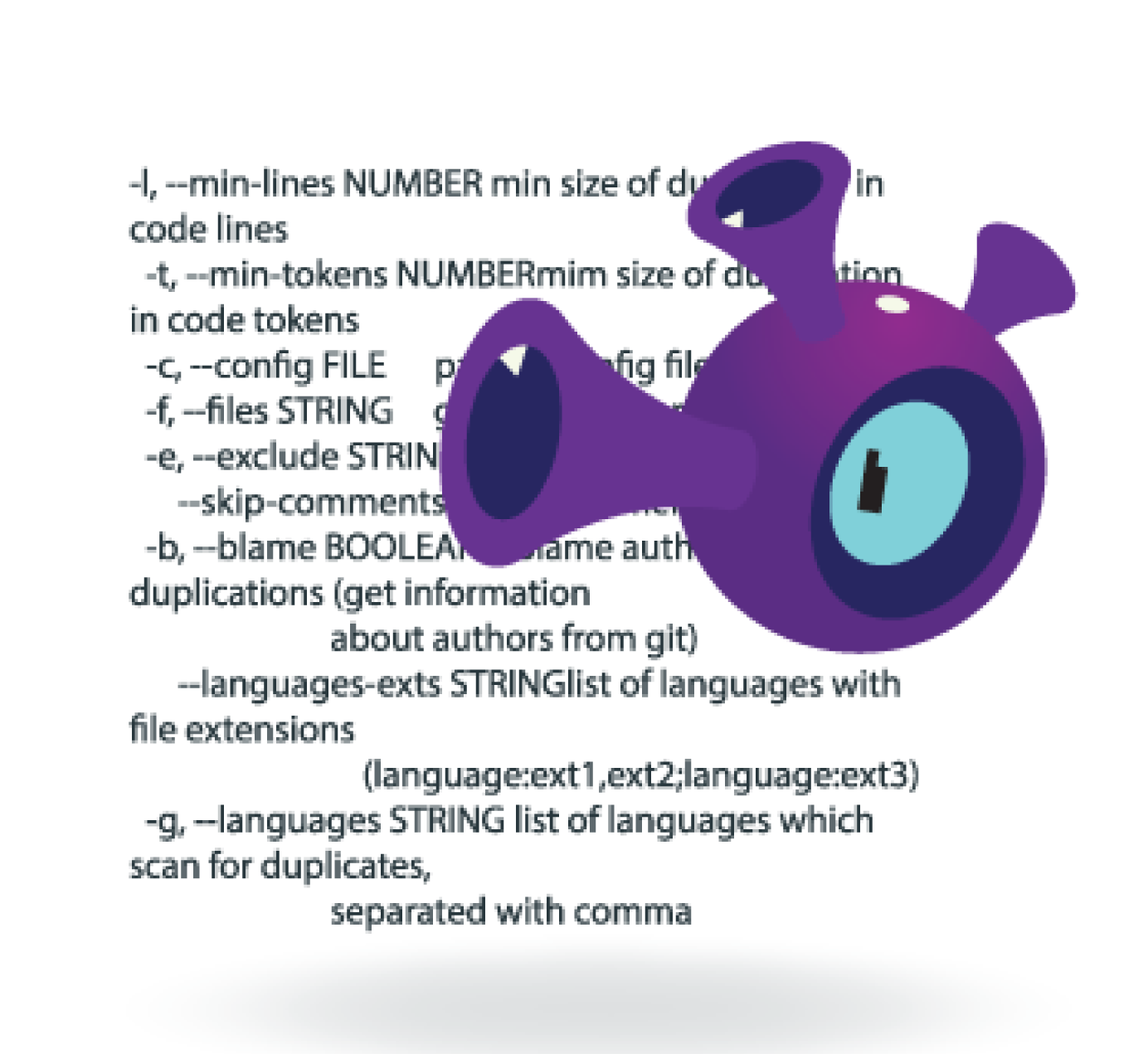
Our application security testing and assessment services include specialized:
- Manual and Automated Testing
- Static/Dynamic/Hybrid Testing
- Advice on how to develop a Secure Software Development Lifecycle (SSDLC)
We deliver the most reliable and cost-effective application security testing services. This helps you ensure that your apps and your brand’s reputation are secure.

BRANDS THAT TRUST US




WHY CHOOSE US?
With our web application and mobile application security assessment services, you can rest assured that your apps are secure.
We understand code and how applications are built.
Most security personnel come from network or infrastructure backgrounds and they don’t understand apps, but we do. All of our security engineers are from development backgrounds. We have developed apps and know the shortcuts developers take. This enables us to secure your web and mobile applications and help you get a secure DevOps pipeline.
We are security experts.
Our engineers regularly instruct for SANS, where they teach developers and organizations how to properly perform security assessments on applications.Using our expertise can help you secure your development lifecycle.
We frequently spread the word about application security.
Our highly-experienced application security assessment experts often speak at conferences and events throughout North America, Europe, and Asia.